ASM CH1 - The context and basis of ASM
1 | This blog is a comprehensive review of the paper [Android Security Model](https://arxiv.org/pdf/1904.05572), based on the content ot the paper, some personal thoughts are also added to this blog including the personal perspective of the author to ASM and the summarization of the content and so on. |
1.1 Android is an opensource ecosystem
In real world, OEM (Original Equipment
Manufacturers) manufactures the products we use such as smartphone, watch and so on. Some of the OEMs aren’t capable of developing the Android components by themselves, so they rely on ODM(Original Device Manufacturers) who’s for hardware and firmware developing, and they are able to modify the Android componets.
1 | Definition of OEM, ODM and OBM: |
Due to this objective situation, AOSP (Android Open Source Program) provides reference implementation for nearly all components (Linux kernel, Trusty, libavb etc.) so that the manufacture can decide which implementation to use based on their requirements.
Two objective facts:
- For users, android treats them as someone with no ideas of any technical knowledge about the system.
- For developers, android provides them with maximum development flexibility, so
- Explicitly supports installation of apps from arbitrary sources, including alternative app stores and apps independently distributed without a store at all.
- Allows applications to be written in any programming language, with or without runtime support, compiled or interpreted.
1.2 Android is defined by compatibility requirements
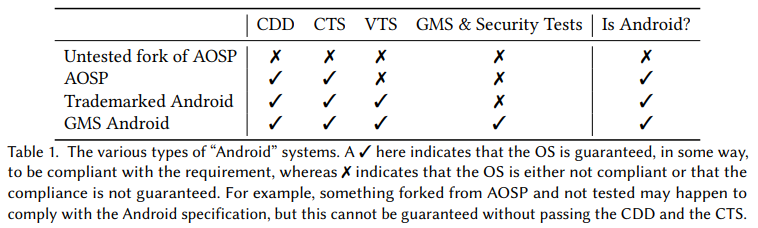
1 | In fact, the Android platform is defined as the set of AOSP components that together form an operating system that adheres to standards called the Compatibility Definition Document (CDD). |
With so many kinds of so-called “androids” system existing, the threat model given in this blog only supports those adhere to CDD&CTS.
1.3 Threat model
There are mainly 4 types of assumed threat models for Android, they are based on the facts that Adversaries can get physical access to Android devices, Network communication is untrusted, Untrusted code is executed on the device and Untrusted content is processed by the device.
Threats due to physical or proximal(P) access:
Level Description T.P1 Adversary has the access to the device (proximal control), they control some of the ways including WiFi, Bluetooth, UWB, FM and so on of the device T.P2 Powered-off devices under complete physical control of an adversary (nation state wise attack) T.P3 Screen locked devices under complete physical control of an adversary (thieves) T.P4 Screen unlocked (shared) devices under control of an authorized but different user (your wife trying to find out your possibly existing messages with other women) network-level(N) threats:
Level Description T.N1 Passive eavesdropping and traffic analysis, based on MAC address or other device network identifiers T.N2 Active manipulation of network traffic (Man-in-the-middle attack, on-path attack or relaying) T.N3 Adversarial cellular network provider (fake cellular base station) Threats due to installation of application(A) code from arbitrary sources:
Level Description T.A1 Abusing APIs supported by the OS with malicious intent, e.g. spyware T.A2 Abusing APIs provided by other apps installed on the device T.A3 Untrusted code from the web is executed without explicit authorization T.A4 Mimicking system or other app user interfaces to confuse users (phishing) T.A5 Reading content from system or other app user interfaces T.A6 Injecting input events into system or other app user interfaces T.A7 Exploiting bugs in the OS to escalate privileges or gain code execution T.A8 Surreptitiously adding potentially harmful code to system images or other code or data executed or interpreted on-device through insider capabilities such as access to private code signing keys Treats from the processing of data(D) and metadata:
Level Description T.D1 Abusing unique identifiers for targeted attacks (spamming or fake official email) T.D2 Exploiting code that processes untrusted content in the OS, firmware, or apps Supply chain attack vectors
Insider attacks
Need to attention that the threat model of “nation state” or “organizational attacks” are not well defined here (since it’s pretty hard to sort out the factors of them), but it’s necessary to take them as part of the realistic threat model.