Forensic Chapter 1 - Preparing for Incidents
1. Difference between Event and Incident
| Event | A cybersecurity event is any observable occurrence in a network or system. |
|---|---|
| Incident | A specific type of event that actually harms or represents a real threat to the integrity, confidentiality, or availability of data or systems. |
For an event, we need to:
- Obeservation: To see if the event is a potential incident or not.
- Take actions: Monitor the situation, review logs and so on.
- Get outcome: Give a conclusion based on the actions.
2. Cyber Incidents Response
Terms
Policy Why we need to do it? Standard What is required? Procedure How to do it? Guideline Customized procedure A sample procedure of CIR
- Rapid Containment
- Reduce Damage and Cost
- Legal and Regulatory Compliance
- Maintain Trust and Reputation
- Learning and Improvement
- Ensuring Business Continuity
Information Sharing
We need to inform some entities when incidents happenning.Idnerify Key Stakeholders
- Internal: within the company, group-level
- supply chain
- regulators
- law enforcements
- within an dcross-sectors
Manage Media Interaction
- designated spokesperson
- timely updates
- flow of updates
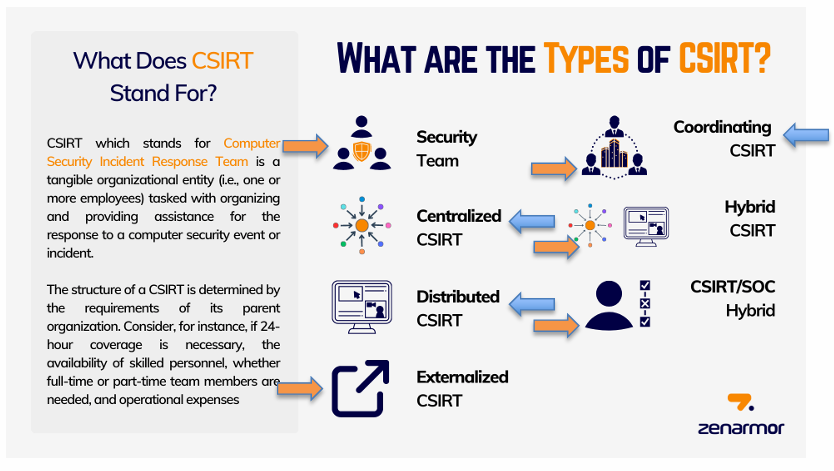
Types of Cyber Security Incidents Response Team (CSIRT)
Security Team
Centralized CSIRT
Distributed CSIRT
Extemalized CSIRT
Coordinating CSIRT
Hybrid CSIRT
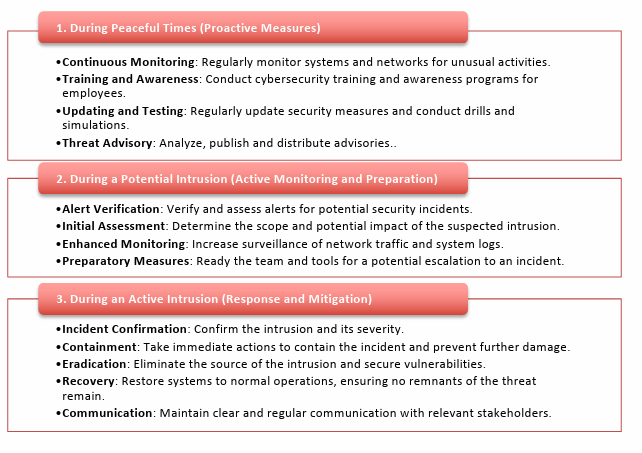
Incident Responders in different periods
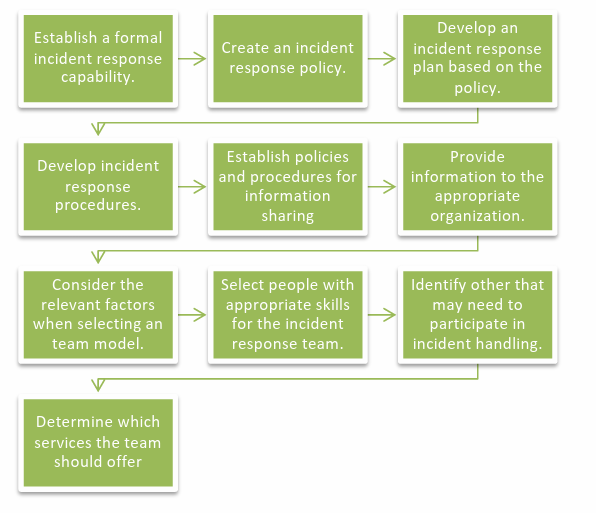
A Recommendation Guideline
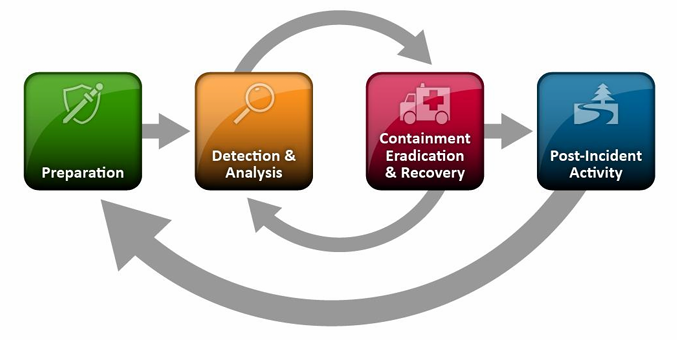
3. Incident Response Lifecycle
Overall Lifecycle
Preparation
Detection & Analysis
Containment, Eradication and Recovery
Post-incident Activity
Preparation (Documentation)
- Asset lists
- Cloud Assets
- Business and System owners
- Others
- Network diagram
- Baselines
- Facility
- Secure storage facility
- Designated War room
- Communication
- Up-to-date contact information
- Mobile phones
- Information sharing platform
- MISP -> Malware information sharing platform
- TheHive
- Computers
- Softwares
- Asset lists
Detction & Analysis
- Know the attack vectors
- Analysis
- Documentation
- Prioritization
- Notification